When you click "lost password" at Steemauto, It will send your password directly to your email. That means, passwords are stored raw in their database.
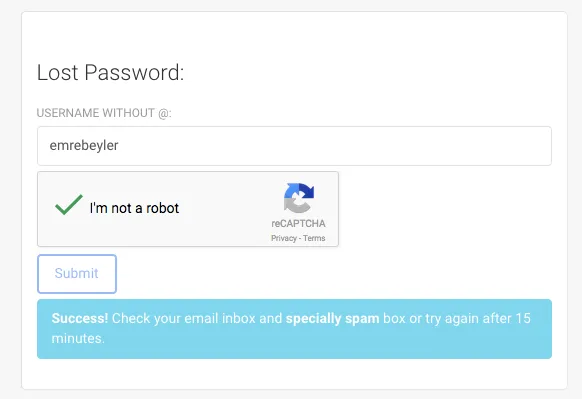
This is one of the sins of web application development practices. If the system can send you back your password, that means the application stores your pasword as plain text..
That's extremely dangerous. If a thief or attacker get the database somehow, they would have every users credentials as well.
Best practice
- Salt and hash each password
- Use good hashing functions like Bcrypt instead of md5 or sha1
- Store SALT + HASH in the database instead of raw password
That way you can't send the password back to users but you may create unique tokens for password regeneration and deal with the recovery as an application developer.
What to do as a user?
Use a throw-away and unique password at Steemauto.
That's the general rule but I am pretty sure %90 of the users, using a generic password that they use on their daily life. If Steemauto database leaks to some bad-minded parties, your accounts will be in great danger.
Edit: @mahdiyari addressed the issue
He removed the username-password authentication and started using SteemConnect for it. Thanks for the fast response!