src

I was trying to understand better how Hive works at a technical level, so I was going through some documentation and exploring the content of blocks. I came across [a transaction](https://hiveblockexplorer.com/tx/8437cffaa71b2fcf292584f19ea407c6dfb40b24] that displayed the user logo at the end of the post text.
That immediately rang a bell. That image should not be there.. only text should be in that table cell!
Therefore I inspected the page and noticed that indeed some text was being parsed by the browser, meaning that it was not correctly sanitized on the server side.
I checked how the post text looked like in the hive block and I crafted a similar comment with some hidden code in it.
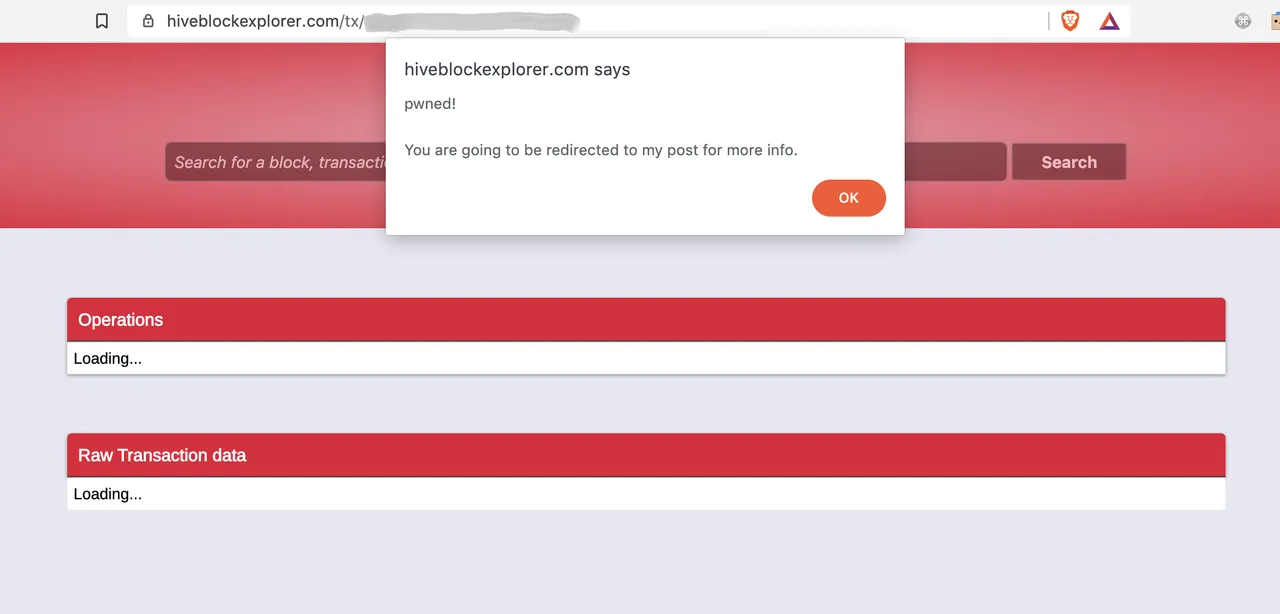
Result: I checked my new comment on hiveblockexplorer.com and the site executed my code!!
- XSS ✅
{{ for more details on what XSS is see: https://www.imperva.com/learn/application-security/cross-site-scripting-xss-attacks }}
Proof:
If you want to check yourself, I stored my harmless XSS herePS. now fixed by @penguinpablo.
If you click on that link:
You will see the alert in the screenshot above;
After 10s you will be redirected to this post of mine.
This happens because the website parses my specially crafted TEXT as code and executed it! That should never happen.
The code stored on that page could obviously be used for evil things like redirecting users to a phishing page!
A user could fall victim of it because a malicious attacker could keep spamming these type of messages into blocks OR, even worse, they could send another user a link crafted in this way as a proof of previous payment, in order to try to steal their private keys.
Guys that maintain hiveblockexplorer.com (@penguinpablo), please fix this ASAP!
Contact me on Discord if you need more details.
#xss #abuse #security #disclosure #shipit #fixasap
UPDATE 1: the same vulnerability is also on steemblockexplorer.com .. but maybe we can leave it like that there. Freaking Justin loves thieves after all..
UPDATE 2: @penguinpablo today fixed the issue: @penguinpablo/qfk9ge
Good stuff!!
Domain now removed from @keys-defender blacklist.
!remove hiveblockexplorer.com
Previous security disclosures of mine:
- Malicious ads injecting code on steemit for all iOS users: @gaottantacinque/steemit-got-hacked
- Reverse tabnabbing and clickjacking: @gaottantacinque/steemit-chat-is-unsafe
